What is Purple Teaming?
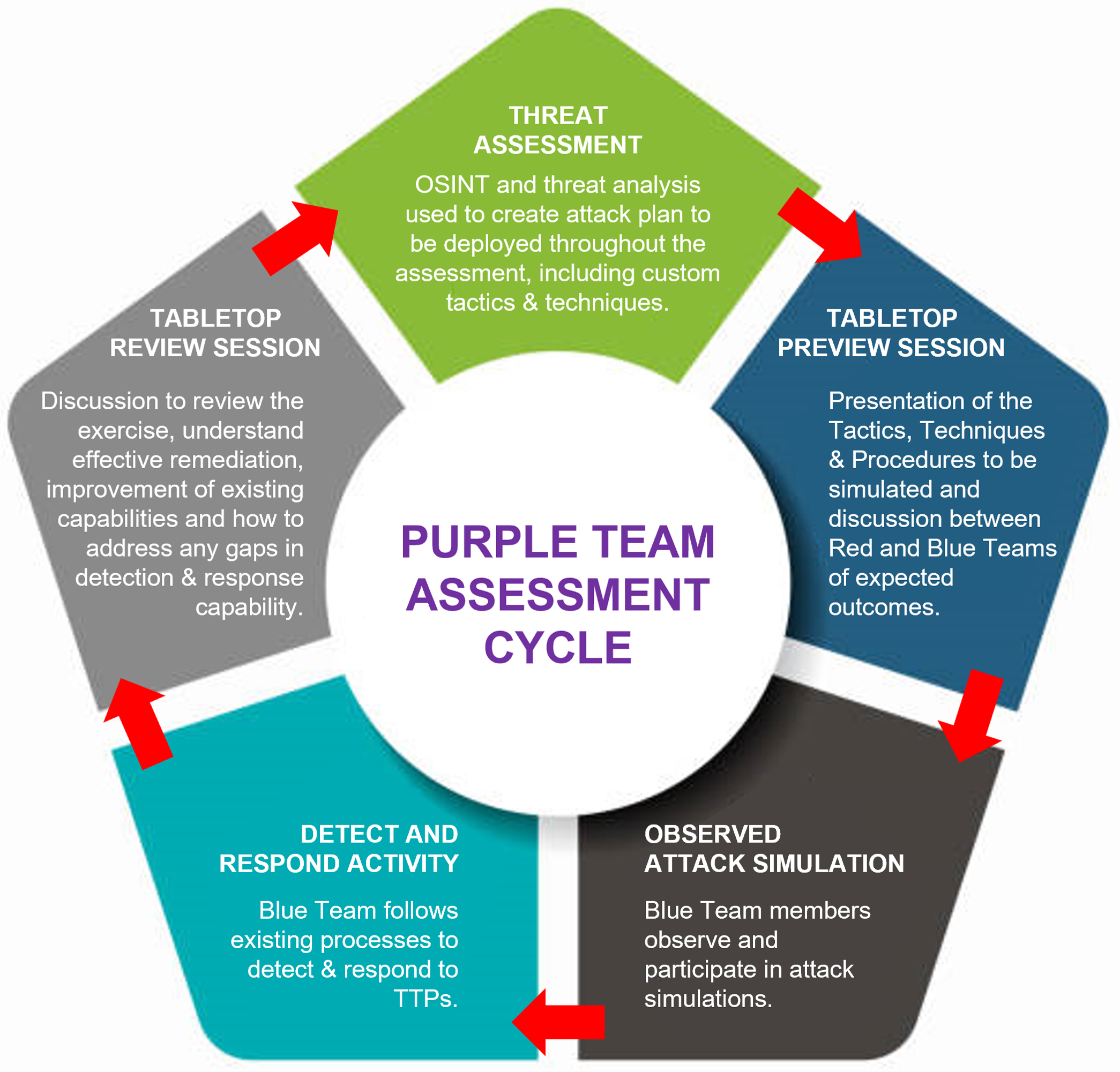
Purple Teaming brings both Red and Blue teams together in a joint exercise which simulates active attack scenarios based on pre-defined goals and identifies gaps and improvements in your security monitoring and defenses. Purple Team Assessments can be applied to the whole organisation, internal assets, the perimeter, or cloud environments.
Effective Assessments
Effective Purple Team Assessments allow you to simultaneously evaluate the effectiveness of your defences whilst improving your team’s capability to defend against real-world attack scenarios.
Throughout a Claranet Purple Team assessment, our experienced Red Team works closely with your defensive Blue Teams to provide continuous feedback and knowledge transfer. Facing real-world attack scenarios, informed by threat intelligence, with the support and guidance of the ethical hacking team, we will help to develop the skills needed by your defensive team to detect attacks, proactively hunt for threats and monitor attack surfaces for suspicious behaviour
Key features
- Bespoke service tailored to your organisation
- Guided discussions & knowledge transfer
- Close collaboration between Red and Blue Teams
- Comprehensive report with executive summary
- Attack scenario details & lessons learned
- Analysis of attacks undetected by Blue Team
- Clear recommendations
- Attack execution log with instructions to recreate exercises
Core benefits
- Test, assess & improve your ability to detect & prevent successful cyber attacks
- Improve and refine the effectiveness of existing security solutions and processes
- Understand where security gaps exist and use the insight to inform buying decisions and security strategy
- Develop an attacker mindset within your defensive teams to better recognize and respond to suspicious activity
How we work with you
We provide a tailored approach based around your objectives, the size and capabilities of your defensive team and the type and sophistication of the attack simulations required. For example, some Purple Team Assessments require extensive knowledge transfer and collaboration throughout attack simulations, whilst others are based on a stealthy, realistic simulated attack delivery with subsequent review and debrief.
This bespoke approach ensures that you receive the right level of support to deliver insight and outcomes that improve your organisation’s ability to defend against cyber attacks.
Our objective is to provide the threat visibility needed for you to make effective changes to security processes, deploy appropriately configured defensive technology and train key staff in a way that will make the job of an attacker more difficult and reduce the chances of a security breach.

Strengthen your security posture with a Purple Team exercise
Book a 1-2-1 consultation
Speak to our team, develop your knowledge, and confidentially discuss your security challenges via a no-commitment 1:1 consultation. Whether it's a specific solution you need more information on or a question you can't find an answer to, we're here
Contact us today by leaving us a message in the contact form and a member of our team will be in touch soon.
Tel: (415) 907-7084
Our accreditations