Attack Surface Monitoring
Complete visibility of your external attack surface, monitored & validated by security experts, with clear monthly reports.
Understand what attackers see - before they act
Your organisation’s external attack surface is constantly changing. New domains are created, cloud services appear, configurations shift, and forgotten assets quietly remain exposed.
Most security teams can only protect what they know exists. Attackers, however, don’t rely on asset lists - they continuously scan the internet to discover weak points, shadow IT, and exposed services.
Claranet’s Attack Surface Monitoring (ASM) service gives you continuous, expert‑validated visibility of your external digital footprint, helping you identify unmanaged risk early and reduce your window of exposure.
ASM runs monthly, tracking change over time and presenting the results in a clear, analyst report - without deploying agents or appliances.

What is Attack Surface Monitoring?
Attack Surface Monitoring (ASM) is a managed security service that
continuously discovers, analyses, and validates the assets your
organisation exposes to the internet — exactly as an attacker would
find them.
ASM identifies:
- Domains and subdomains
- IP addresses
- Open ports and services
- Cloud and internet‑facing infrastructure
- Shadow IT and forgotten assets
Findings are reviewed and validated by experienced security analysts
to remove noise and highlight what genuinely requires attention.
Why Attack Surface Monitoring matters

Digital transformation, cloud adoption, CI/CD pipelines, and M&A
activity have dissolved the traditional security perimeter.
Organisations now expose more assets, across more platforms, than ever before.
Without continuous visibility, this creates risk in the form of:
- Unknown or unmanaged external assets
- Shadow IT introduced outside formal governance
- Misconfigurations and exposed services
- Compliance and audit blind spots
- Increased cost and scope for security testing
ASM helps you regain control by providing persistent visibility, change
awareness, and evidence‑based insight into your real‑world exposure.
How the service works

Claranet combines specialist discovery tooling with human‑led
analyst validation to cut through the noise and focus on meaningful
risk.
Each month, we:
- Discover internet‑facing assets across your external environment
- Identify changes, new exposure, and unmanaged resources
- Validate findings to reduce false positives
- Deliver a clear, actionable analyst report
Optional Quarterly Business Reviews provide deeper trend analysis
and alignment with your wider security strategy.
What you get
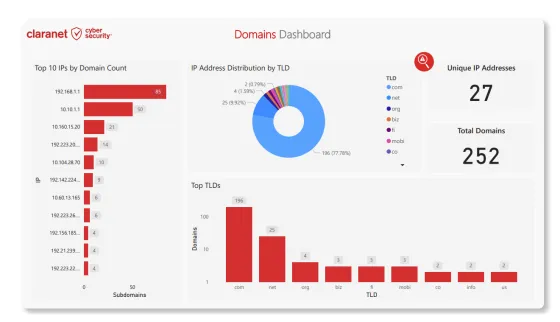
Continuous discovery of domains, subdomains, IPs, ports, andservices
Shadow IT detection across cloud and decentralised environments
Human analyst validation to reduce noise
Monthly security reports
Optional Quarterly Business Reviews
No agents or appliances required
Standalone or bundled with Continuous Security Testing, vCISO,SOC or any of our cybersecurity services
ASM + CST
Organisations using a Continuous Threat Exposure Management (CTEM) program will be about three times less likely to experience a breach
Attack Surface Monitoring and Continuous Security Testing (CST)
address two different — but complementary — stages of exposure
management.
- ASM ensures you know what is exposed
- CST continuously tests those exposed assets for exploitable
vulnerabilities
Together, they provide true Continuous Threat Exposure Management
(CTEM) and form a critical part of External Attack Surface
Management (EASM) — discovering new risk as it emerges, testing
assets continuously, and validating remediation over time.
ASM helps ensure CST is always focused on the right assets, reducing
noise, lowering testing cost, and maximising security return.